Microsoft saved NATO countries from hacker attack
18. August 2022Microsoft saved NATO countries from hacker attack
San Francisco, 18.8.2022
Microsoft has shut down a Russian state-backed hacking group called Seaborgium before it could carry out its planned attacks on targets in Nato countries.
Seaborgium also goes by the names Callisto Group, ColdRiver, and TA446. The hacking group has directed most of its attacks at targets in the U.S. and U.K., but is also known for attacks on other European countries.
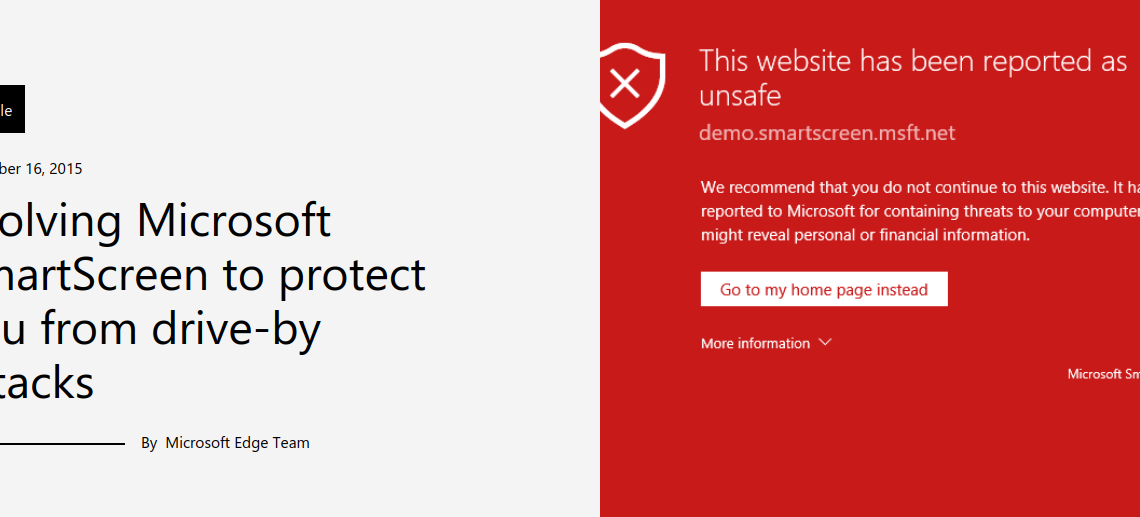
To counter the attack, Microsoft said Aug. 15 that it had disabled accounts used by the „Seaborgium“ group for reconnaissance, phishing and email collection and updated the detection of its phishing domains in Microsoft Defender SmartScreen. That group has attacked more than 30 targets in recent years, it said.
Seaborgium is a „very persistent threat actor,“ Microsoft stressed. The group operates primarily in the U.S. and the U.K., with only occasional activity in the Baltics and Nordic and Eastern European countries….
After scouting its targets, the group tries to establish a relationship with the potential victims. For this purpose, the hackers prefer social media . Shortly after, a phishing email is sent, supposedly containing content of interest to the recipient.
Malicious URLs may be in the body of the email, a clickable button used to open an attachment, or a OneDrive link that takes the user to a PDF file with a URL.
Regardless of the delivery method, when the target clicks on the URL, they are directed to an actor-controlled server that hosts a phishing framework, most commonly EvilGinx. Once the target is redirected to the final page, the framework prompts the target for authentication by mirroring the login page of a legitimate provider and intercepting all credentials. After the credentials are captured, the target is redirected to a website or document to complete the interaction.
Once Seaborgium has access to the victim’s email account, it attempts to exfiltrate intelligence data and occasionally contact other persons of interest through these compromised accounts to obtain sensitive information.
Sometimes it even sets up forwarding rules for the victim’s inbox to enable persistent data collection, Microsoft said.


